Executive Summary
CVE-2025-55182, commonly known as React2Shell, is a critical unauthenticated remote code execution (RCE) vulnerability affecting React Server Components (RSC) and modern frameworks built on top of them, including Next.js App Router.
While the vulnerability was publicly disclosed by the React security community, the Hiperlinx Cybersecurity Research Team conducted an independent proof-of-concept (PoC) to deeply understand the exploit mechanics, attacker tradecraft, and real-world exposure patterns. Based on this research, the team authored custom real-time detection logic inside Mitral ASM, enabling identification of React2Shell exposure and exploitation across the external attack surface at scale.
This write-up documents the vulnerability, its impact, and how organizations can mitigate it—while highlighting how Mitral ASM operationalizes detection beyond traditional scanning approaches.
| For more information, request a free trial for Mitral ASM on https://mitral.io | |
1. What Is React2Shell (CVE-2025-55182)?
CVE-2025-55182 is a design flaw in React Server Components’ Flight protocol that allows attacker-controlled serialized payloads to be unsafely deserialized and evaluated on the server.
The flaw resides in the following React packages:
react-server-dom-webpackreact-server-dom-parcelreact-server-dom-turbopack
Any framework embedding these components is affected, including:
- React 19.x Server Components
- Next.js 15.x / 16.x (App Router)
Because the vulnerable logic executes before authentication and application routing, exploitation is trivial for any internet-exposed deployment.
2. Hiperlinx Research: PoC and Exploit Validation
To accurately assess real-world risk, the Hiperlinx Cybersecurity Team developed a controlled proof-of-concept exploit against a vulnerable Next.js environment.
PoC Findings
- Exploitation requires no authentication or session state
- A single crafted HTTP request triggers server-side execution
- Payloads are processed during React Server Component rendering
- Arbitrary JavaScript executes with full Node.js process privileges
- Post-exploitation actions (file access, outbound callbacks) are immediate
This PoC confirmed that React2Shell is not theoretical—it is weaponizable, reliable, and highly scalable for attackers.
3. Impact: Why React2Shell Is High-Risk
Once exploited, React2Shell enables complete compromise of the application server.
Attack Outcomes Observed and Modeled
- Arbitrary command execution
- Theft of environment secrets and credentials
- Database access and data exfiltration
- Persistent backdoor installation
- Internal network pivoting
- Deployment of cryptominers, tunneling tools, or ransomware
Because the vulnerability is pre-auth and server-side, traditional controls such as login protection or user-level monitoring offer no meaningful protection.
4. Detection with Mitral ASM
React2Shell highlights a critical reality: you cannot protect what you cannot see.
Using insights from the PoC, the Hiperlinx team authored custom detection logic within Mitral ASM to identify React2Shell risk and exploitation in real time.
Mitral ASM enables organizations to:
- Continuously discover internet-facing React and Next.js services
- Fingerprint vulnerable RSC versions without authentication
- Detect exploit attempts via anomalous Flight protocol payloads
- Correlate exploitation signals with post-exploitation behavior
- Track exposure across thousands of assets simultaneously
Unlike periodic scanners, Mitral ASM operates continuously, matching the pace of attacker reconnaissance and exploitation.
React2Shell is a clear example of why attack surface management must function as a live detection system, not a scheduled compliance check.
| For more information, request a free trial for Mitral ASM on https://mitral.io | |
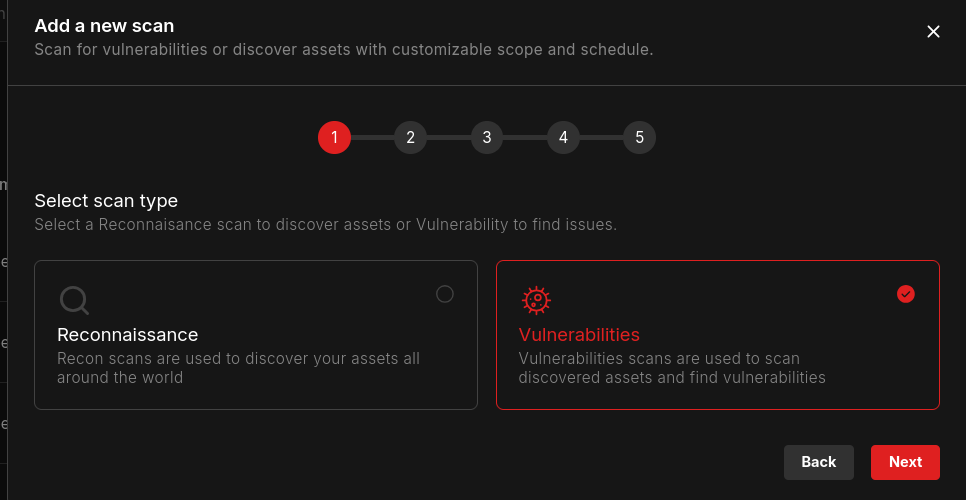
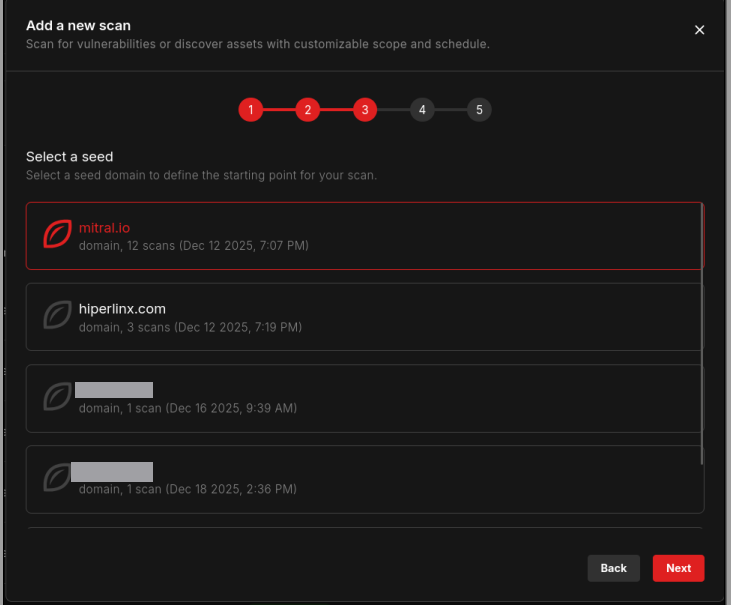
STEP 1
From the Mitral ASM Admin Dashboard, create a new vulnerability scan.
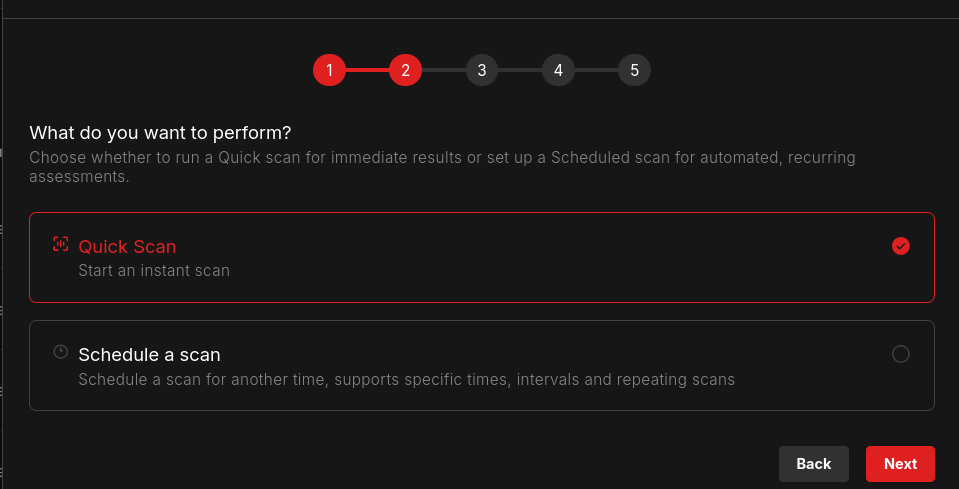
STEP 2
Choose between a quick scan or scheduled scan accordingly to your company policies to run vulnerability assessment activities.
STEP 3
Choose the seed to scan
STEP 4
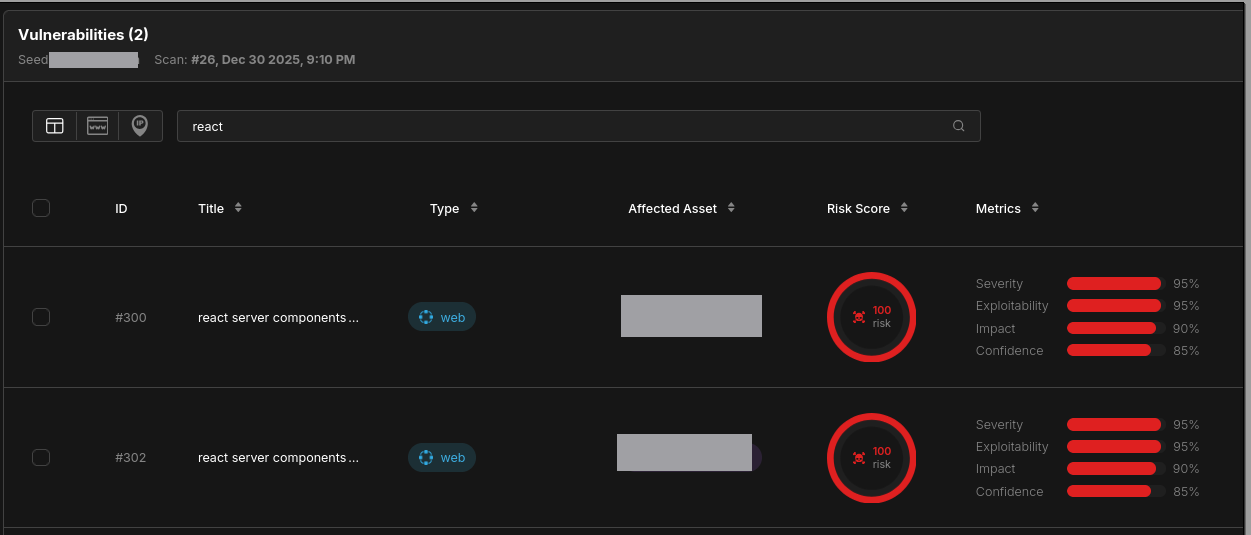
Select the assets you would like to scan

STEP 5
Successful vulnerability detection listed in the vulnerabilities table.
| For more information, request a free trial for Mitral ASM on https://mitral.io | |
5. Mitigation and Remediation
5.1 Patch Immediately
All affected systems must be upgraded.
React Server Components
Upgrade all react-server-dom-* packages to patched releases (≥ 19.2.1).
Next.js
Upgrade to one of the following versions or later:
- 15.0.5
- 15.1.9
- 15.2.6
- 15.3.6
- 15.4.8
- 15.5.7
- 16.0.7
Any unpatched deployment remains trivially exploitable.
5.2 Defense-in-Depth Controls
Even after patching, the Hiperlinx team recommends:
- Strict validation of RSC request payloads
- WAF rules targeting malformed Flight protocol traffic
- Least-privilege execution for Node.js services
- Outbound network restrictions
- Monitoring for abnormal child process execution
Mitral ASM continuously validates whether these mitigations actually reduce external exposure, not just internal risk assumptions.
6. Why React2Shell Reinforces the Need for ASM
React2Shell did not succeed because defenders ignored security—it succeeded because most organizations lacked visibility into their real attack surface.
Key lessons from this research:
- Modern frameworks introduce non-obvious, fast-moving attack surfaces
- Pre-authentication RCEs bypass traditional assumptions
- Asset inventories are incomplete by default
- Scan-based security does not match attacker speed
Mitral ASM was built to address exactly this gap:
continuous, external, real-time detection of exploitable conditions as they emerge.
| For more information, request a free trial for Mitral ASM on https://mitral.io | |
7. Conclusion
CVE-2025-55182 (React2Shell) is a high-impact vulnerability with real-world exploitation and minimal attacker cost. Through hands-on PoC research, the Hiperlinx Cybersecurity Team translated exploit mechanics into practical, scalable detection inside Mitral ASM.
React2Shell is not just a React issue—it is a visibility problem.
Mitral ASM turns that visibility into actionable security.
| For more information, request a free trial for Mitral ASM on https://mitral.io | |
Hiperlinx Cybersecurity Research Team